CanadaCyber has identified a recent e-mail phishing attacks,
targeting Canadian Hotmail users.
The e-mail comes in titled as:
You received INTERAC e-Transfer Or You received a tax refund
The email looks like this on a phone then a laptop.
The e-mail is simple you get message that looks like a standard
email money transfer via INTERAC something that many Canadians are accustomed to.
The amount of $214.17 is also a number that a lot of families in Canada are
used to receiving from their federal government from GST to Child money.
When you click on the Deposit your money link it fwds you to
a page that is asking you for your password. When you place your password it
collects your password then it moves you to the next stage of the attack.
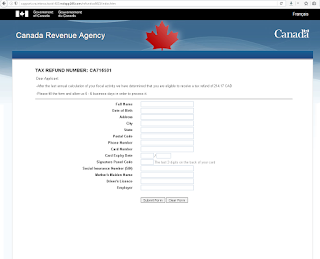
At this stage you think all is good as you see the normal government
of Canada web site. You then go on and place more information like your PII Personally identifiable information and
banking information. After that you are thanked, at this stage the BAD Guy has
all of your info. Then you are redirected to the real government of Canada revenue
agency website. So now
they have your passwords and all of your information.
The e-mail it self has a embedded png file ejuiceejuice.com/image/data/etransfer2 the interesting thing is the server used to host this image is diff than the landing page.this could be due to the attacker just linking to the file directly or using different servers for different jobs. this way it would be much harder to talk him down. as you have to contact 3 diff providers.
The e-mail it self has a embedded png file ejuiceejuice.com/image/data/etransfer2 the interesting thing is the server used to host this image is diff than the landing page.this could be due to the attacker just linking to the file directly or using different servers for different jobs. this way it would be much harder to talk him down. as you have to contact 3 diff providers.
the above screen shows the landing page for the first stage it send you http://support.cra.interac.taxid-423.redapp244.com/secure/index.php?em=somename@hotmail.com, we can see this is not hotmail or outlook.com from the URL. if we do a dns lookup on the URL we do see it from217.160.0.192 belonging to 1& 1 shared hosting account that is hosting almost 1500 websites. this means any of these website could been exploited to do this but it is likley redapp244.com was compromised and the attacker created a subdomain with the name support.cra.interac.taxid-. On a mobile device this would fool most users as it does look like it is CRA.
On the 2nd stage we see the attacker is trying to mimic/clone a real CRA page. they even change the title header to look so. in both 2nd stage and 1 stage the attacker used the landing page server for the links redirection and content.
Now we analyze the e-mail by looking at it source:
We see it came from a shaw.ca cable IP address 24.70.214.97
in Calgary; this could be the attacker or a compromised workstation working on
his behalf. We then see it doing to the smtp-out-so.shaw.ca @ 64.59.136.138,
also in Calgary. We suspect this server is allowing mail forwarding from
trusted IP’s as the source IP is from the SHOW.ca network.
This is the first mistake SHAW.ca did, it trusted its
internal users IP range. Shaw.ca also did not confirm the email sender X-SID-PRA was notif482@grs.trustwave.com this is
clearly not a shaw domain name or a show e-mail sub-domain. This is even more dangerous
as the average user looking up this www.trustwave.com
gets to see a legitimate security business, something that will later on help
in convincing the victim to click on the link that will later on harvest his
password.
Again this is due to Shaw not confirming the sender e-mail
address so the mail severs they use just fwd the e-mail even if the email sender
is forged.
The e-mail is crafted to gain your trust first after it collects
the most valuable item your PASSWORD
it then moves on as it knows you might even give away more info like your PII,
address, name banking info. Anything they need to fully steal your identity.
Canada Cyber had also submitted the url to virus-total and only google safe browsing identified it as bad. https://www.virustotal.com/en-gb/url/26ae24d8a6e5bdad3cdf9bf8bbf8c78dbe89b4d4df96fb058f526a7bde680be1/analysis/1472437103/
This new attack is similar to this: http://globalnews.ca/news/1900959/canada-revenue-agency-warns-of-recent-scam-involving-money-transfers/
Canada Cyber had also submitted the url to virus-total and only google safe browsing identified it as bad. https://www.virustotal.com/en-gb/url/26ae24d8a6e5bdad3cdf9bf8bbf8c78dbe89b4d4df96fb058f526a7bde680be1/analysis/1472437103/
This new attack is similar to this: http://globalnews.ca/news/1900959/canada-revenue-agency-warns-of-recent-scam-involving-money-transfers/
CanadaCyber